To understand why we don’t need SMS 2FA, we’ll order the factors from least secure to most secure.
- Password
- Password + SMS 2FA
- Password + Authenticator App
- Unique Password
- Unique Password + U2F
*A unique password is a reasonable length, random, and never reused password.
Password – Affected by phishing attacks, credential stuffing attacks, malware, and brute force guessing.
Password + SMS 2FA – Affected by phishing attacks, SIM Swapping, $16 exploit, SMS password resets, malware, and doesn’t solve credential stuffing attacks.
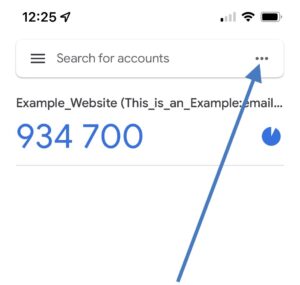
Password + Authenticator App – Affected by phishing attacks, malware and doesn’t solve credential stuffing attacks.
Unique Password – Immune to credential stuffing attacks, Immune to phishing attacks if autofill is used but affected by malware.
Unique Password + U2F – Immune to credential stuffing attacks, Immune to phishing attacks, affected by some malware but has better odds compared to everything else.
Why Have 2 Factors When 1 Will Do?
Using a Unique Password is better than using a Password + SMS 2FA.
- Is immune to credential stuffing attacks, unlike Password + SMS 2FA.
- When used with autofill it protects against phishing, unlike Password + SMS 2FA.
- Cheaper than SMS 2FA for both the user and the service.
- Helps fix user’s bad habits of reusing passwords.
- Requires fewer steps and complexity.
- Doesn’t require 3rd party support.
A Unique Password protects you from more attacks than SMS 2FA.
| Attack | Unique Password | Password + SMS 2FA |
|---|---|---|
| Credential stuffing | Not Affected | Affected |
| Phishing | Autofill, Not Affected | Affected |
| Brute Force | Not Affected | Affected |
| SIM Swapping | Not Affected | Affected |
| SS7 Exploits | Not Affected | Affected |
| SMS Reset | Not Affected | Affected |
| Malware | Affected | Affected |
| Server Breach | Affected | Affected |
There is no benefit to have Password + SMS 2FA when a Unique Password is overall better.
Half the reason why SMS 2FA gets implemented is to fix the password reuse problem… but 2FA is not an excuse for password reuse!
Consider The Grandma Test
What’s easier…
Having grandma write down 3FD-8DD-AC4B in her password book?
Or…
Having grandma remember which one of her reused passwords she picked and what was that app with the 2FA code? Then waiting for the code to come and knowing what to do if it doesn’t come.
- SMS 2FA doesn’t solve the password reuse problem; she continues her bad habit.
- SMS 2FA doesn’t protect her against phishing.
- SMS 2FA is another thing she needs to figure out.
- SMS 2FA is something else for her to lose.
- SMS 2FA is something else that can stop working.
- SMS 2FA creates new points of attack against grandma, for example, SMS 2FA password resets.
SMS 2FA isn’t helping grandma; it’s making it worse for her.
Having grandma write down a generated password is vastly simpler, more accessible, cheaper, and more secure than SMS 2FA will ever be.
Unique Passwords > SMS 2FA + Any Password
There is no benefit to having SMS 2FA when a unique password is an option.
Combined with the fact that you can’t use the internet without a web browser and every web browser offers to save and fill passwords for you, it just makes sense to use unique passwords.
The most popular browser is Chrome, and it works on all devices. Chrome saves, fills, and generates passwords. Google does a better job of securing your account than your phone provider will ever do. Google themselves don’t rely on SMS 2FA due to its vulnerabilities.
Yet, people still fight to keep SMS 2FA.
The only reason to keep SMS 2FA is if you want to track your users. Maybe that’s why it’s still around?
Read More
Tavis Ormandy: You don’t need SMS-2FA – https://blog.cmpxchg8b.com/2020/07/you-dont-need-sms-2fa.html
PasswordBits – https://passwordbits.com/dont-need-sms-2fa/


This totally misses the point of 2FA. It’s called two factor for a reason: 2 steps to enter an account is better than one. If one is compromised, the other stands in the way. Of course, it’s no substitute for not having unique passwords, but this is NOT the whole point about 2FA. One step to access an account is a risky procedure. For example, a simple keylogger exploiting a future update vulnerability in Windows would be able to compromise your “unique” password and use it to enter your bank account, if it wasn’t for 2FA. SMS 2FA has it’s disadvantages, as everything in life, but it adds a layer of security.
Two factors are better than one unless both factors can fall for the same attack. Both a unique password and SMS 2FA can not protect you against malware, it’s a losing battle.
If the attacker has installed a keylogger or any malware they have control over the computer, they can do whatever they want. They can force the computer to go any phishing site to perform a Modlishka like attack and get around 2FA. They can steal the session cookie or remote into the computer. They can get the password and 2FA code and stall your computer while a remote computer logs in before you.
SMS 2FA does not protect against keyloggers and malware. You can read more here under the heading “Vulnerable to malware / keyloggers” https://www.allthingsauth.com/2018/02/27/sms-the-most-popular-and-least-secure-2fa-method/
Not only does SMS 2FA not protect against malware but it can open new points of attack with SMS resets.
I would argue that in many cases Bad Password + SMS 2FA is actually WORSE than just a bad password, because SMS 2FA almost always comes bundled with SMS password resets, leaving you open to all the SMS-based attacks you wouldn’t be vulnerable to even if you reused the same crappy password. You have next to no extra benefit and a LOT of extra vulnerability.