Password requirements keep getting more complicated as the years go on.
It used to be simple, 5 characters minimum. Then it was 6, then 8 but with a capital and a number.
Today, it’s not unheard of to have password rules of 15 characters minimum along with uppercase, lowercase, numbers, and special characters.
When does the madness stop?
5 years from now, are we going to make users have a 20 character minimum password? 30? 40? There has to be a better way?!
Why Do We Have Password Requirements?
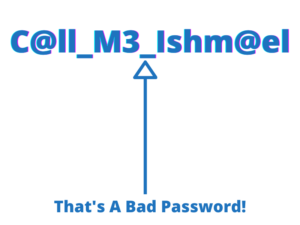
The original goal of password rules was to keep users from using simple passwords like “12345”.
Today, password requirements are used to keep users from reusing passwords. If your go-to password is 8 characters long, it’s hard to reuse it on a service that has a minimum length of 10. Password reuse is a far bigger problem, and making password rules more complicated keeps you ahead of this problem.
But this created a new problem – there is no endpoint.
We can’t keep making password requirements more complicated and longer forever.
We’re at a point where it’s not uncommon to see a password requirement of 15 characters minimum along with uppercase, numbers, and the whole shebang.
To get a job at the USPS it requires you to have a password that is at least 15 characters long that you must change every 90 days.
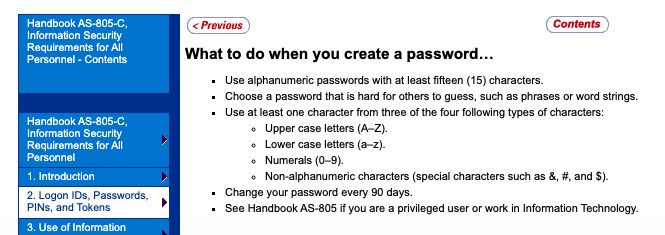
The creators of the Discourse forums force a 15 character minimum on admins and moderators… “Since I wrote that, we’ve already increased our minimum password default length from 8 to 10 characters. And if you happen to be an admin or moderator, we decided the minimum has to be, even more, 15 characters.”
That link above is from the site CodingHorror.com, and it’s a great read. I loved it because he says password requirements are bullshit, and I agree. The best part was that he was looking to make it simple but kept running into exceptions to the rules, which complicated things more. He never talks about the simplest and most effective approach that will solve all of this, generate the passwords for users.
At What Point Do We Generate The Passwords For Users?
No, seriously, at what point is it easier to generate the password for users?
Generating passwords for users is not that crazy; I go over why here.
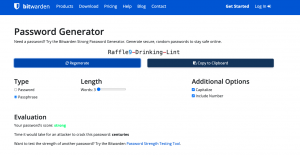
We can generate simpler and more secure passwords than what most complicated password requirements require of users.
The user-created password Appl3Tr33P4$$21 and the randomly generated password 692-A27-A4DA both have 44 bits of entropy, but the randomly generated password is shorter and easier to read or write. The randomly generated password is a hexadecimal number and the same length as a phone number which people have no problem storing.
Just 10 years ago, an 8 character minimum password was seen as a lot. Today, we have 15 character minimums. 10 years from now, will it be a 25 character minimum?
If password requirements are used to combat password reuse and weak passwords, why don’t we cut to the chase and generate the passwords for users?
Password Requirements Are Stressful
Password requirements are stressful – it puts you on the spot, forces you to overthink, burdens you with having to remember something else, and you often have to try 3 different passwords before the site accepts one.
Password requirements are like asking someone to solve a math problem on the spot (12559 * 4674). Generating the password for the user is like telling them the answer to the math problem (12559 * 4674 = 58,700,766).
Instead of asking someone to follow crazy steps, we just give them the result we want.
No real thinking involved; write it down or store it in a password manager and move on.
There is a certain relief when you get things out of your head and onto paper. You’re removing the burden and freeing your mind for more important tasks. It’s the same feeling you get when you put your goals or a to-do list on paper.
Passwords Need To Be Stored, Not Remembered!
The problem is not the password itself but the way we have taught people to store them.
People think they need to remember passwords.
This is not possible or reasonable. The average person has 100 passwords, that is 100 passwords following 100 different password requirements. It’s no wonder people hate passwords.
It’s okay to write your passwords down. It’s okay to keep your passwords in a password manager. It’s not possible for you to remember every password, nor should you; you’re only human.
No one gets mad at you because you can’t remember every phone number in your contact list. So why are you burdening yourself with remembering passwords?
What about using 2FA? Here’s the interesting part about 2FA like TOTP; what makes it so secure is the same point I’m making in this article.
Just Let The Users Use Weak Passwords?
I see users get upset when they can’t use their weak passwords.
They don’t understand why they can’t just sign something that allows them to use their bad passwords and remove liability from the service?
It’s not that simple.
Your account getting breached will affect others on that service too. No one wants to use a service that keeps getting breached because users like to use poor passwords. Weak passwords cause services real issues; remember the Ring Security Camera Hack? That was because users were allowed to use weak and reused passwords.
“But I still don’t care“… you’ll start caring quickly when your hacked account starts doing something illegal and the cops come after you. Accounts are stolen every second to push political agendas, marketing, or to do illegal things. What’s not important today doesn’t mean it won’t be important later.
What blows my mind is that no one has this energy for other things. No one complains about not being able to pick…
- Serial numbers
- Phone numbers
- Credit card numbers
- Activation codes
- Birthdays
- Account numbers
- Social Security Numbers
You simply store this information and move on.
Are you mad that you didn’t get to pick the phone number of your local pizza restaurant? No, you stored it in your contacts list and moved on. So why are passwords any different?
I find it funny when I come across someone complaining a site won’t let them use their weak reused password. To me, it’s like seeing someone complain they can’t get VISA to change their credit card number to 12345 to make it easier for them to remember. A credit card has 16 digits you did not get to pick and yet they don’t complain about it but will complain they can’t use 12345 password for everything – it makes no sense. Just store the password like you store phone numbers and credit cards and move on.
Why Do People Burden Themselves With Remembering Passwords?
The reason is simple: they’re not aware or told about password managers or writing passwords down.
For years “experts” have been telling users not to write down their passwords. As if allowing the user to reuse the same password for Netflix as they do for the company online portal was any better.
The only threat writing down passwords has is anyone who can physically access the paper of passwords. Someone breaking into Nana’s house and stealing her passwords out of her cookbook is a minimal threat.
Not allowing someone to store passwords causes them to reuse passwords. Reusing the same password results in multiple points of attack. Instead of worrying about that one piece of paper, you now have to worry about that password being used on numerous accounts spread throughout the world on computers you don’t control. One could argue it’s better to have all your eggs in one basket to minimize multiple points of attack.
When you generate the password for the users, it gets them in the same mindset of phone numbers. They look for ways to store them, manage them, and optimize for them. This all happens without telling them, just like how password requirements have trained people to make strong passwords; password education happens at the sign up pages!
Its A Matter Of “WHEN”, not “IF”
What is clear is that password requirements will only get worse.
It’s not a matter of “IF” we’ll generate passwords for users but a matter of “WHEN”.
There will come a time where generating the password for the users will be the easier route. Even if the user refuses to write the password down, you can still have the password reset feature, and you ultimately have magic links and everyone is still better off.