There has never been a more important time to protect one’s accounts from cybercrime, than ever before. Sometimes, a username and password is not enough, you need an extra layer.
This extra layer goes by two-factor authentication (2FA) and it’s a huge help in protecting your online accounts.
We have many types of 2FA on the market, from an SMS message to your phone, email message, Google Authenticator or even a physical key. While they all have their advantages, are they enough to stop hackers? Like most things, that depends, there is one type of 2FA that gets pretty close, but we need to cover it in more details. Let’s go down the rabbit hole on 2FA security and how it may or may not protect you from cyber-hackers.
What is 2FA
2FA is two-factor authentication, it’s the text message, email, or app that you use after you enter your password.
Most people know it by the text message or email you get when logging into a website, but there are other options like an app or a physical security key.
Websites will use something you know (your password) and something you have (2FA) to confirm you’re the right person logging in. While a password can be guessed, leaked, stolen, etc., proving you have something is much harder to fake and thus why we use 2FA.
While 2FA seems great, there are many conditions that come with it that doesn’t make it “hacker-proof”.
Why 2FA Doesn’t Make You Hack Proof?
There is one type of 2FA, called U2F, that will get you pretty close to being “hack-proof”, and we’ll cover that later on, but first we’ll cover all the other types of 2FA and how they don’t help much.
Here are the types of 2FA:
- SMS 2FA
- Email 2FA
- Push 2FA
- Grid 2FA
- App-based / TOTP (Google Authenticator, Authy, Duo, Steam, etc.)
- U2F
Here are the list of reasons why 2FA doesn’t make your hack-proof, and we’ll go into more details about them later in the post.
- 2FA doesn’t stop reverse proxy attacks.
- 2FA doesn’t stop replay attacks.
- 2FA codes can be easily guessed.
- 2FA doesn’t stop man-in-the-middle attacks.
- The 2FA device or network can be compromised.
- 2FA is more as a band-aid on the password problem then actual 2FA.
Let’s explore each of these points!
2FA Doesn’t Stop Reverse Proxy Attacks
I put this one at the top because it’s the most shocking to people, especially those who use app-based 2FA like Google Authenticator or Authy.
A reverse proxy attack is quite simple, you’re tricked into going to a website, but that website acts as a web browser and loads the actual website you want to go to. You’re actually going to the real website, but the attacker’s website is acting as the web browser for your web browser.
So when you log in, you’re logging into the real website, but the attacker’s website gets the cookie, knows the password and can now do whatever they want. They could turn 2FA off, as many websites allow you to turn it off once you’ve logged in and know the password.
All types of 2FA, expect U2F, will fall for this attack. Not even Google Authenticator or Authy app-based 2FA can protect you from this attack.
To give you an idea of how bad this attack is, here is someone using it to get into a password manager even with app-based 2FA on the account:
It’s kind of scary!
This is why it’s important to double-check the URL before logging in and to use a password manager to autofill the passwords for you. A password manager would not fall for this trick, as the URL needs to match what you have stored before it will fill the password.
2FA Doesn’t Stop Replay Attacks
A replay attack is someone getting your password and 2FA and then using it again, often very quickly, to also log in behind you or before you.
You may fall for a fake phishing site and give them your password and 2FA. Most 2FA expires after a certain time, some may be minutes while others like app-based 2FA is seconds.
If it was app-based 2FA, like with Google Authenticator, the attacker has anywhere from 30 seconds to 90 seconds of that code being good. That is like 30 days to 90 days in the computing world because of how fast they move. So if you end up giving your password and 2FA code to the wrong website, they have plenty of time to log in and do what they want on the real website.
And once they’re in the account, 2FA is not always needed to turn it off or do whatever they want.
If the attacker controls the network, they could delay your communications and let theirs go first, just in case the website has checks in place.
All types of 2FA, but U2F, will fall for this attack. This means email, SMS 2FA, Google Authenticator, push notification, and more!
2FA Codes Can Be Easily Guessed
In 2019, an exploit was found on Instagram that allowed an attacker to guess all combinations of SMS 2FA code and reset the account password and get them in the account.
Not only is SMS 2FA the worst type of 2FA, but far too many websites allow you to bypass everything and get in the account with just an SMS password reset code.
The problem is that the 2FA codes that are most used are only 6-digits long, that means there are only 1 million combinations. That is not many combinations, a computer could go through all of them in minutes if the service has no or little rate-limiting in place.
The same is true with app-based 2FA, they’re only 6-digits long, and if you already know the password then only 6 numbers are keeping you out. This is why 2FA is not an excuse for bad passwords!
2FA Doesn’t Stop Man-In-The-Middle Attacks
A man in the middle attack is when an attacker is “ease dropping” on to your communications.
The reverse proxy and the replay attacks fall under this type of attack too, an attacker could watch you enter your password and 2FA and do a replay attack. If the attacker controls the network, they can also delay your communications or take over what you’re doing and log in after you submit everything.
This is why VPNs have become so popular, but they’re kind of overblown and oversold, especially when a website uses HTTPS. I’m not saying they’re completely useless, but they are oversold on what they do.
The 2FA Device or Network Can Be Compromised
Something that doesn’t get enough attention, but no 2FA can help you if your computer is compromised. That even goes for U2F!
Once you’ve logged in with your password and 2FA, you now have full access to the account and so does any malware on your system.
Most websites put a session cookie on your computer, it works similar to a long password that proves you are the correct user, and these cookies can last hours if not days depending on the website. For example, once you log into something like Twitter you may notice you don’t have to log in for days, if not months, if you keep using the same device and browser, as it’s using a cookie to auto-log you in.
If no extra protections are in place, the attacker’s malware could grab that cookie and send it off to the attacker. Another option is to do what they need to do remotely to your computer, but this is more obvious and not always the most ideal way.
Cookie Stealers are a very common attack and often leaves many people dumbfounded as they had 2FA on their account, but never realize 2FA does nothing to protect you from malware and other viruses.
When I say 2FA does nothing, I mean no 2FA, not even U2F, can protect you. Once you logged in then 2FA is not needed anymore and the rest is up to the website to do its checks to make sure the cookie is not being used from a different computer.
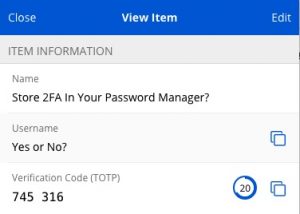
2FA Is More Of A Band-Aid On The Password Problem
More of a personal pet-peeve is that far too many people are using 2FA as an excuse to keep using bad passwords.
When I say bad passwords, I mean reusing the same or similar password. Not only does this defeat the point of having two factors, but it’s an overcomplicated way to have a password manager.
Once you understand how 2FA like TOTP works, you start to realize it’s just a password manager but done poorly. It also creates extra unneeded steps for the user and creates more misunderstandings.
2FA is never an excuse to use bad passwords!
U2F 2FA
I’ve made a couple of mentions of U2F, it’s a type of 2FA but uses a physical key.
This type of 2FA can also go by WebAuthn or FIDO2.
Of all the types of 2FA, a physical security key used for U2F is the best option we have today.
- U2F won’t fall for phishing attacks, as the website’s URL is used in the authorization process. Wrong URL, wrong code, and you can’t log in.
- The private key is embedded into the device and can’t be copied, unlike other 2FA. It’s the most 2FA we have, it’s proof you have the device, and it’s not anywhere else in the world.
- It doesn’t rely on an open (and often unencrypted) medium to transmit the code to you like SMS or Email 2FA.
- Replay and man in the middle attacks don’t affect it.
- Websites only store the public key of the of this Yubikey, which is fine and useless anywhere else. It’s like giving people a padlock, a padlock can only be locked and otherwise useless without the key, and that key never leaves the Yubikey. So, a website getting compromised doesn’t mean you need to change your physical key.
- And its security is so good that it’s being pushed as a password replacement with WebAuthn.
- Google themselves use it, and it’s stopped ALL phishing attacks on them.
The only thing U2F can’t protect you against is malware, but nothing would. Once your computer is infected, it’s not your computer anymore. I suggest reading our tips here to keep your computer secured.
The most popular U2F keys are made by Yubikey and you can get them here (Ad). I suggest getting two of them, so you have a backup. Most services allow you to add multiple keys to your account. If the account gives you a backup code, be sure to write that down and keep it somewhere safe. Just remember each key doesn’t relate to another, you must add each one to an account for them both to work.



Push notifications done with apps are out of band, so avoid replay. Then again users may just think the popup notification is a glitch and say yes twice…