I don’t know how I ended up with so many Yubikeys, but I guess it’s to be expected with how much I like digital security.
As I was sorting through them, figuring out which ones to keep and which ones to give away, a question popped into my head. If I give Yubikeys to family or friends, and they notice I have many of them, are they going to be worried that they need a lot of them too?
Better yet, I know a few of them will ask if you can use one Yubikey for many logins, or will they end up like me as a “digital janitor”? I’m sure many of you have the same question, and the answer is not so cut and dry. That is why in this post I want to answer this question and more, so let’s get right to it!
What Are The Accessibility and Versatility Of Yubikeys?
One common misconception about Yubikeys, and hardware keys in general, is that they are complex and cumbersome to use, designed only for tech enthusiasts or those with advanced security needs.
However, the reality is quite the opposite. Yubikeys are designed with simplicity and ease of use in mind, making them accessible to everyone from tech novices to cybersecurity experts.
The process of setting up and using a Yubikey is straightforward, involving just a few steps to link the device with your accounts, thereby significantly enhancing your security with minimal effort.
What Is A Yubikey, And How Does It Work?
A Yubikey, a hardware authentication device (hardware key), authorizes you with websites or services. It acts as a second authentication step post-password entry.
Websites that support them offer an alternative to text or email codes.
Hardware keys, compliant with WebAuthn, allow passwordless logins by replacing traditional passwords. Compact and similar to USB thumb drives, they attach conveniently to keychains, like house keys.
Is One Yubikey Sufficient for Numerous Accounts?
A YubiKey supports an unlimited number of accounts with both WebAuthn and U2F protocols.
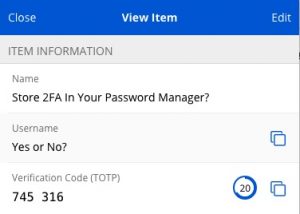
If you’re using your hardware key for TOTP, you can only hold 32 accounts.
What Is WebAuthn, And Why Does It Matter ?
WebAuthn, a FIDO Alliance initiative, offers a secure login standard using a security key for websites and apps.
It’s safer than traditional usernames and passwords and is supported by popular browsers such as Chrome, Firefox, and Edge.
It’s a collaborative effort by companies to establish a unified standard for using physical security keys in login.
We Need To Cover TOTP
TOTP, or Time-Based One-Time Passwords, is a type of 2FA.
A 6-digit code is created using current universal time and a shared secret, acting as a means to verify your identity.
These 6-digit TOTP codes change every 30 seconds, boosting security by regularly expiring.
While TOTP and WebAuthn both serve 2FA purposes, WebAuthn is notably more secure.
Why Is There No Limit On WebAuthn, Unlike TOTP?
Hardware keys supporting TOTP (Time-Based One-Time Passwords) have storage limits due to capacity constraints.
TOTP involves a secret key, a shared randomly generated password known to the user and server. When combined with the current time, it produces a 6-digit code. These keys have limited storage, capping the number of TOTP 2FA secrets.
WebAuthn, however, operates differently with public and private keys, as we’ll discuss next.
How WebAuthn Works
WebAuthn enables unlimited account storage as it avoids needing extra key data storage.
Your hardware key houses a private key, securely within the device, and a shareable public key. Think of the public key as unlimited open padlocks and the private key as their unique key.
When registering on a website, you only share the public key, with data storage handled by the site, eliminating user storage worries.
For login, the site sends a challenge based on your public key, like a math problem. The server expects the correct response, generated solely with the right private key.
As the public key comes from the private key, the correct solution confirms your identity, proving possession of the matching private key.
Is WebAuthn More Secure Than TOTP?
WebAuthn surpsses TOTP in security since it solely involves sharing a public key with the server. Consider this public key as an open padlock; anyone can secure a message with it, but only the holder of the private key can unlock it.
Adding an extra layer of protection against phishing attacks, WebAuthn incorporates the website’s URL into the process. Consequently, each service you use with WebAuthn possesses its distinct public key.
Therefore, a security breach on one service won’t jeopardize your identity on other services using the same hardware key.
You Need To Get Two Security Keys!
Hardware keys and WebAuthn boost security, but have limitations.
One drawback is the need for two separate devices or keys. OSes like Windows, Mac, Android, and iOS support this standard, letting your phone or computer serve as the primary device, but a backup key is important.
Without a recovery option in some services and lacking a backup key, you risk permanent lockout.
Another WebAuthn challenge is balancing secure recovery. Strong security can be compromised by weak recovery methods, yet serrvices must offer recovery options due to user errors.
Security keys aim to safeguard the private key from external extraction, a security measure. However, this limits backup options.
The best solution is maintaining a few security keys for backups.
Are There Other Keys?
There are many kinds of hardware keys, some of them already built into your phone or computer.
You also have Solokeys which I like and support the FIDO2 standard.
The Solokey is an open-source hardware key that is worth giving a try. It works just like any other hardware key and far more trusted because of its open standard.
Does A Yubikey Protect You From Being Hacked?
While a Yubikey uses Webauthn, which is one of the most secure options we have, it doesn’t protect you from being “hacked”.
When I say hacked, I mean it doesn’t protect you from malware on your computer. If your computer is infected, they don’t need your password or any auth. It’s like worrying about putting a lock on your door when the burglar is already in your home.
It can protect you when the service is breached as the only thing stored on the server is a public key and, as we know, it’s pointless for the attacker to have unless they wanted to send you a secure message.
Why Are Hardware Keys Not Used For Cryptocurrencies Like Bitcoin?
If you can store unlimited accounts with your Yubikey, why don’t they use that for cryptocurrencies and other things that need to be locked?
The reason is that these online services are about doing a test to confirm you are the right person. They’re not about scrambling the information so that only the right person can see it.
Bitcoin and other cryptocurrencies use public and private key encryption, and it shares a lot of what a hardware key does, but it’s not exactly the same. The WebAuthn is just a different flavor made for logging to online accounts and not securing digital assets.



Best explanation I’ve seen.