A common trend I see is the rush to turn on 2FA like Google Authenticator and Authy, but do people understand why it’s so effective?
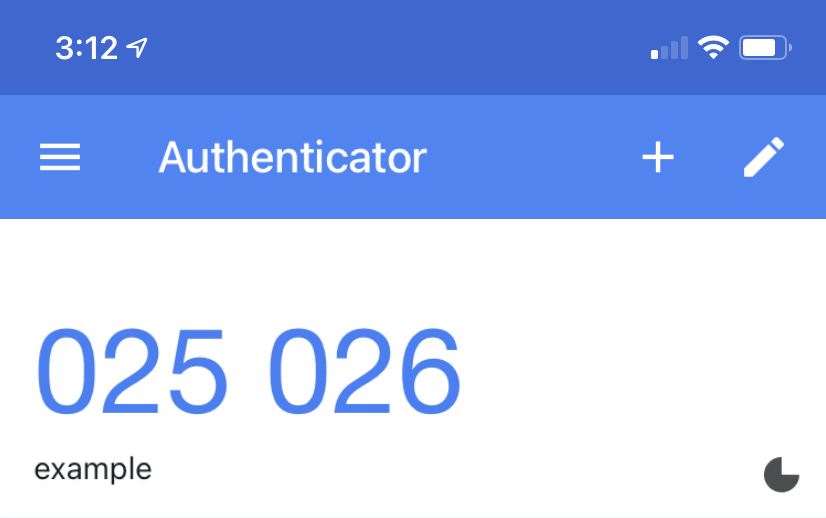
Google Authenticator and Authy are TOTP (Time-based One-time Password) 2FA.
I’m going to show you what makes TOTP 2FA so effective and why this matters.
How TOTP 2FA Works
When you turn on TOTP 2FA, you’re shown a QR code that looks like this.

A QR code is a way to transmit information to a computer from the real world or a non-connected device like your phone. Go ahead and open your phone’s camera app to scan the QR code above.
Inside that QR code contains text that looks like this.
otpauth://totp/This_is_an_Example:email@email.com?algorithm=SHA1&digits=6&issuer=Example_Website&period=30&secret=S6HZS7XT6KQ6AFSR7XEVO
Within that text, it tells the TOTP app what kind of 2FA it is, username, the secret, and the website URL. This info is added to your 2FA app, and the app generates the ever-changing 6 digit code.
The most important part of that string of text is the secret (secret=S6HZS7XT6KQ6AFSR7XEVO).
The TOTP Secret
In our example, the secret is S6HZS7XT6KQ6AFSR7XEVO.
The secret inside of TOTP 2FA is nothing more than a randomly generated password.
That secret is combined with the current time to give you the 6 digit code you see that changes every 30 seconds. Anyone who knows that secret can put it in any TOTP app and generate the same 6 digit codes as all TOTP 2FA devices go off the universal time.
Yup, it’s that simple.
What makes TOTP 2FA so effective is the randomly generated secret (aka password). If we allowed people to make their own secrets, we would have the same problem we have now with people reusing passwords (credential stuffing attacks).
The very act of not letting the user create their secret is what makes TOTP so great!
Why This Matters
This matters because not every website will ever implement TOTP 2FA or any 2FA at all.
It’s unfortunate but true.
But you don’t need to worry because you can get the benefit that TOTP 2FA supplies by merely using a password manager.
Instead of waiting for a website to implement 2FA, you can today get a password manager and use it to generate and store a random password that you use for login. As we’ve learned, what makes TOTP 2FA so special is the fact that the secret is a random password.
If you don’t trust password managers, I have a solution here that solves that.
But 2 Factors Are Better Than One!
Yes, 2 factors are better than one.
The problem is that many services and users use 2FA to solve their password reuse problems.
If your first factor is already known because of password reuse, then you don’t have 2FA anymore but instead 1FA with an extra step. It’s just like having a door with two locks but you keep the PIN code visible for the first lock on the door – you effectively have one lock protecting your door.
That’s the irony of the whole situation.
Turning on 2FA to fix your password reuse problem is not solving the actual problem. You’re applying a bandaid – TOTP 2FA – and what makes it strong is the secret which is a random password. If a TOTP 2FA app stores random passwords, then it’s nothing more than a password manager.
You’re jumping through all these hoops to ultimately end up with random passwords in a password manager. If that is the case, then why not do that from the start? Especially when a website doesn’t support 2FA, you can still do a random password from your password manager and still be just as good.
Simply giving every account it’s own random password would solve most of your “hacking” problems. To say this is not true would be like saying TOTP 2FA is not going to solve it either.
It’s Passwords All The Way Down
The secret inside of TOTP 2FA is nothing more than a random password.
Not only that, but the backup codes you’re given to turn off 2FA if you lose your device is random passwords too.
Even the secure U2F keys have a private key, which is just another type of password.
It’s passwords all the way down, and this is why passwords are here to stay. The quicker people realize this and adopt things that make this easy, like password managers, the better off they’ll be.
Why Don’t Websites Generate The Password For Users?
If the strength of TOTP 2FA comes from the fact the user never creates the secret, which is nothing more than a password.
And that password is generated by the service, then why don’t they generate the password for the user from the start?
I agree.
That is why I wrote this article about why they should.