I’m seeing way too many people using this line when it comes to getting their accounts “hacked”…
“If only service ______ had 2FA I would have never gotten hacked!!!”
As if 2FA (2 Factor Authentication) is some magical cure to hacking.
You got hacked because you used a weak/reused password, not because some company did not have 2FA. If you’re the type of person to have a weak password would you also be the type of person who would use 2FA? It’s easy to say yes after the fact, but in reality, someone who uses a weak password would never opt for 2FA. I know this for a fact because if you were the type of person to use 2FA you would also be the type to have a unique password from the start and your account would not be hacked.
“Weak Password” – If you reuse a password it instanly becomes weak. It doesn’t matter if the password has uppercase, lowercase, numbers, or even special characters. Password reuse is the way accounts get hacked in the real world.
2FA Is Not A Magic Cure
Using 2FA doesn’t give you an excuse to use a weak password.
A weak password used with 2FA is like having a door with two locks, but the first lock’s key is under the welcome mat.
Why would any sane person do this? Why would you do the same thing for your online accounts?
2FA is meant to be a second factor, so your first factor needs to be good too. If your first factor is a weak password, then you never had 2FA, but instead, you have 1FA. Even worse, you have 1FA with twice as many hoops to jump through – enter the password then 2FA code.
The Issue With 2FA
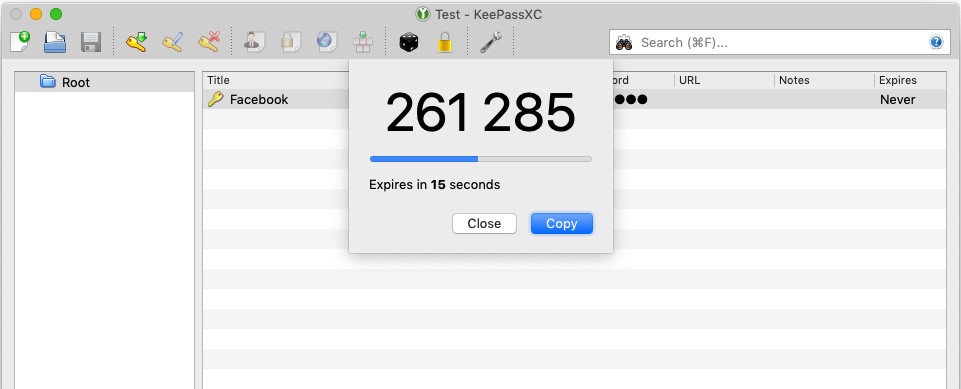
While 2FA seems simple, the majority of people find it complicated to grasp and don’t realize the ramifications of losing the 2FA codes.
Even the people who “get it” still get it wrong. Many of them don’t know apps like Google Authenticator don’t back up their 2FA codes so if they get a new phone or lose their phone they don’t have their codes anymore. That is by design by the way. It’s supposed to be something you have and backing it up to the cloud broadens the attack surface making 2FA not as secure as it needs to be.
Unless you print out the QR codes or save the secret, it’s not being backed up. These extra steps are why so many people don’t want to fuss with 2FA and why so many websites don’t implement it either.
There are options like Authy that allow you to back up your 2FA to their servers, but it requires a password. Not the best option as the weakness is behind a password and phone number. It’s also something else to set up and remember which adds to the drag of having 2FA.
The more friction there is for 2FA the less likely people will use it. Not only is their friction with setting up 2FA but there is literally an extra step to use it.
The Worst Part of 2FA
The worst part of 2FA is how effective it can be. If you lose your phone and don’t have a backup of the codes, it can be a painful process of getting back in if you can get in at all.
If it’s not a painful process can we claim 2FA is helpful?
For example, with iCloud, if you forget your password and don’t have access to one of your Apple devices to confirm via 2FA, it can take days if not weeks to get your account back.
If it was as easy as answering some questions like “what is the name of the street you grew up on” then your 2FA is only as secure as the answer to those questions.
What about the many sites that once you lose your 2FA no one can help you. If you’re not responsible enough to make a unique and strong password from the start will you be responsible enough to have a back up of your 2FA?
What it all boils down to is you making a good unique password from the start.
It Always Leads Back To You And Passwords
It will always lead back to using a unique and strong password. It doesn’t matter if you have 2FA or not.
Your problem is not that they don’t have 2FA but that you don’t use unique passwords and don’t have a safe place to store those passwords.
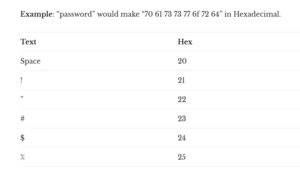
You need a central location that you trust to store all your passwords. This is called a password manager and if used correctly can solve most, if not all, of your password and account issues.
And I know many of you don’t want to use them because of all the eggs in one basket, one device to now hack and protected with only one password – but I have several guides to help you here.
The solution is that simple; get yourself a password manager. Give every account a unique password no matter how unimportant you think it is. Use a strong master password for your password manager. And most importantly, write down your master password so you won’t forget it.
It’s time to stop blaming websites for what they SHOULD do and instead you do something that you CAN control.