It blows my mind that all these websites that talk about the most secure password managers on the market never seem to talk about the actual most secure password manager.
To be honest, the most secure password manager today is free, so I’m guessing that is why so many refuse to talk about it, as there is no kickback.
Also, the most secure password manager is not the best overall password manager.
There is a lot to unpack here, but if you only care about the MOST SECURE password manager, then keep reading.
The Most Secure Password Manager
The most secure password manager you can get is KeePassXC.
Visit KeePassXC website here: https://keepassxc.org/
As someone who loves another password manager called Bitwarden, which I recommend to most everyone that asks, KeePassXC just edges them out in the security department.
I consider Bitwarden the best all-around password manager, especially for the average person, but if all you care about is the most secure password manager then KeePassXC is the answer.
Why is KeePassXC the most secure password manager?
- It’s open-source.
- The vault is local.
- Many KDF options (Argon2).
- Additional encryption options like Twofish and ChaCha20.
- Key File.
- Yubikey/OnlyKey challenge-response support.
- Highly customizable password generator.
- It doesn’t download favicons by default.
- TOTP Storage.
- File attachments.
Let’s go through each point to show you why KeePassXC is the most secure password manager.
1. It’s Open Source
Open source means anyone can view the code.
This keeps things transparent and open for anyone to view. So if the programmers decide to do bad things, people will know.
It also has the benefit of the “many eyes on the code,” and the more eyes you have on something, the more people can find bugs and problems. This is called Linus’s Law.
While open-source code does not always guarantee it being more secure, it’s still better than closed source code, as we at least can see it.
This builds trust in the application, which lends itself to being secure.
2. The Vault Is Local
KeePassXC, just like most password managers, has a vault that keeps all your passwords. To protect this vault, password managers use your master password to encrypt the data.
Some password managers like Bitwarden, 1Password or LastPass will store your vault on their servers. This is not a huge deal for some as they don’t know your master password and thus store a bunch of useless information.
KeePassXC, on the other hand, doesn’t have a central server to store your vault. The KeePassXC vault is stored locally or where ever you want it.
You can store it on a flash drive, your computer, Dropbox, or even the moon if you can; it’s up to you.
Having the flexibility of where your vault gets stored is a huge win for security, but only if you can handle the responsibility.
3. Many KDF Options
Key derivation function (KDF) is a technique to make your master password harder to guess without requiring too much effort from you.
A lot of password managers, especially online ones, use a KDF that is called PBKDF2 SHA-256. PBKDF2 is quite good and the standard.
But KeePassXC defaults to Argon2d, which is vastly better than PBKDF2.
And it not only defaults to Argon2d, but it also allows you to increase iterations to make it even stronger.
Argon2d is a slow hashing algorithm, and the slower the hashing algorithm, the longer it takes to guess your master password.
Cracking a password that uses PBKDF2 SHA-256 is challenging but doable. But cracking a password that uses Argon2d makes you want to give up before you even start. Argon2d is not impossible to crack, but it sure is more annoying than PBKDF2 SHA-256.
4. Additional Encryption Options
The standard encryption that most everyone uses is AES or Advanced Encryption Standard.
Most password managers use AES256 bit encryption, often called “Military-Grade Encryption.”
AES256 is quite good, but some don’t like it because they think it was created by the NSA and assume it has some kind of backdoor. This is just crazy talk and not true at all.
What happened was that Rijndael, its original name, won a competition in 2001 for being the encryption standard we have today. The US government adopted it for their own use, and thus why many password managers throw around “Military-Grade Encryption.”
AES is tried and tested, and thus why it’s the standard that is used.
But sometimes, not being standard is what you want, and KeePassXC gives you other options besides AES.
KeePassXC also has TwoFish and ChaCha20 encryption options.
Are they better? Well, that depends on who you ask.
They are different, which you could argue is better. More people use AES, so the greater the need to break it, and if it does break, you’ll be glad you use something else. But also, the more people trying to break it and fail, the more secure AES becomes. Though, you have to wonder if someone does break AES, will they brag about it?
Either way, having the options are for sure better.
5. Key File
Since KeePassXC is a local password manager, it can’t benefit from normal 2FA as you need a central server for that.
Instead, KeePassXC uses a key file as a substitute.
A key file is just like any other file; it can be a text file, a picture, or even a video if you want. The file contents are added to the end of your master password and used to encrypt your vault.
Since you don’t need to remember the contents of the key file, they can be very complex. You store the key file separately from your vault, such as an external USB flash drive. When you need to log into your vault, you enter your master password and plug in your flash drive so KeePassXC can read the key file and unlock your vault.
You will need your master password and key file to unlock KeePassXC if you’ve set it up that way. Of course, you can run KeePassXC without a key file if you want, but having one makes your vault a lot more secure.
There is extra responsibility with using a key file, for example, if you lose it, you will be locked out. Or, if the key file is changed in any way, it can lock you out.
6. Yubikey/OnlyKey Challenge-Response Support
A Yubikey or OnlyKey is a physical key that you plug into your computer for 2FA, but you can set up a Challenge-Response so it can also be used to unlock your KeePassXC vault.
You can use the Challenge-Response feature to further secure your KeePassXC vault. So when it’s time to unlock your vault, you enter your master password and must also use the security key before the vault unlocks.
The great thing about the Challenge-Response option over a key file is that you’re less likely to mess it up and thus it is reliable.
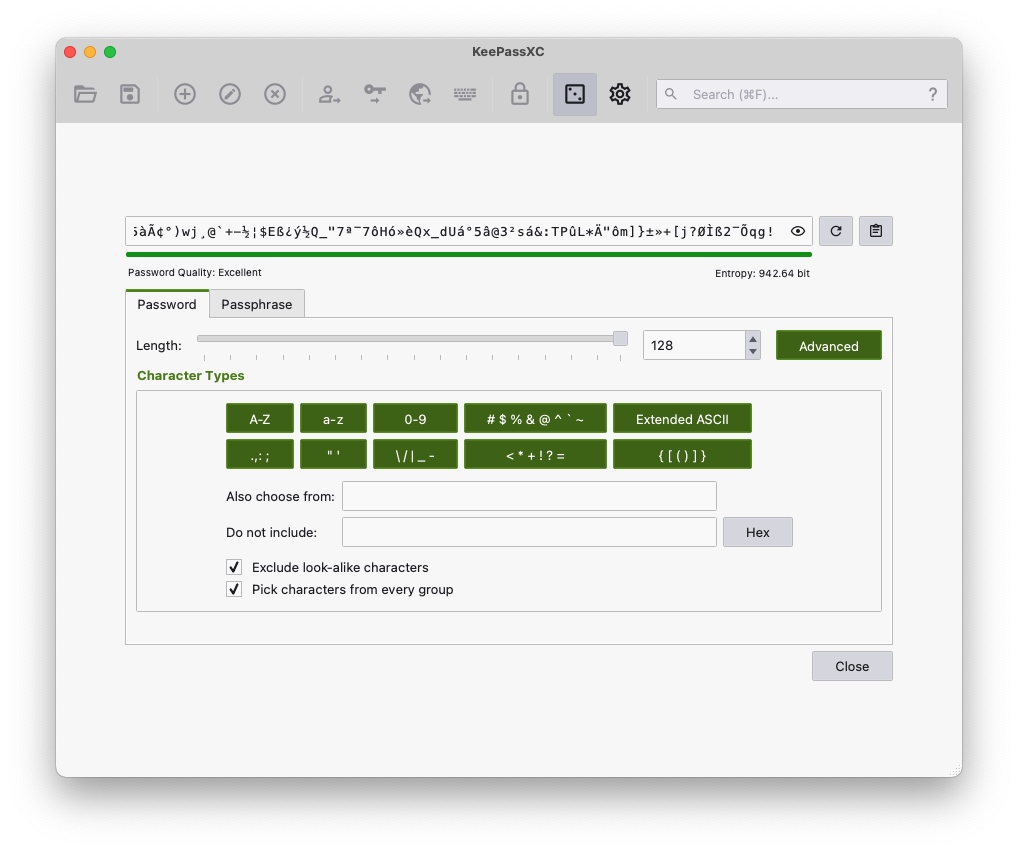
7. Highly Customizable Password Generator
I’ve never seen a password manager with as many options for a password generator as KeePassXC has.
We have the options you expect like…
FPs>S!veM=7ch?ex?+aW
But it can get even crazier with more special characters like…
PwYK~[dnE<_H,9'"<o\^
That is not even the full scope, as you can use extended ASCII characters to get passwords like this…
&¿ïÚ_K¢âeÂ?³5³," <ðR}
Passwords like this may break some websites and are not something you should use a lot, but having the option is great. A password like this would make for a great key file or a local encrypted backup password for VeraCrypt.
And the way KeePassXC allows you to make overly long passwords means you can take it to the extreme…
Ãíª}P´Çk¹n~ò¤Ò]ØvÎ\cÆ×ÎìñKÛ>Er'F:£ê@áEè}çåÒ=ļV_4U?!f¸fo¬^DåçzÃ%¨@Îͧ¯d"NÔè½ì$jP¨¬rEèE¦ÝØ.ÛjȺ/µbéTÀ·²%W´ÌêÒ/þN©HÃMøt{¹eÉö[òp}ìÒ£X"ínÎ=kÇ3b:ÄSvCFF¨õ7®ÀnÎÂ[xT.=²¾h£[ÛhÜR¬büee÷Àýk(Ê÷}wØmжy«¶±ã·Ñ½N7_?®"³ÅâC9;k-Ï}'bÙð¶Ðx-äMÐARÓóN¹ígãRtÕ¡ÂCp©sw+^öØi`NH÷#.}C:ཹÈa¢pZ#(WïÉS~":~3Q¥ÞÆáðNNn~Ð/ünË¡!$YR_ühH¸ÿÿ4!ÉY]÷Re^¬%©þ_NÖj«ñeJÿÿzÊ9á&Â}ÖÝqÂÙÛ©!»×HðɱV©z(iX!7þs=§hɳMéÙCUÀé¼^=i·ÆÊ~xT/R-¬
And they have options for passphrases like…
nervy-dyslexic-sermon-unboxed-rippling-afflicted-punch-sabotage
The most secure password manager needs some overly secure password generators to go along with it, and KeePassXC checks that box.
8. Doesn’t Download Favicon’s By Default
A favicon is the little site icon often located in the tab of your web browser.
Here is the one for this site.

Many online password managers will download the favicon for each item in your vault to make it look pretty and easier to pick out accounts. Some do it better than others, but overall, they all need to call out to some server somewhere to get this image.
Calling out to a server could be an issue for some, especially ones that need to take security to the extreme.
KeePassXC not reaching out to grab these icons by default is a super important feature that must not go unnoticed.
It’s not bad that other password managers do it, but for some people, their threat level just doesn’t need another thing to worry about.
9. TOTP Storage
TOTP is a type of 2FA, more often known by Google Authenticator or Authy.
This is a 6 digit code that changes every 30 seconds.
Many password managers can store TOTP codes but often charge extra for them. KeePassXC gives it to you for free.
While keeping your TOTP 2FA in your password manager is a very hotly debated topic, as talked about here, KeePassXC gives you a nice loophole.
With KeePassXC, you can have as many vaults as you want, which means you can have one vault for your passwords and another for your TOTP codes.
And since you can store the vaults where you want, you can get creative and keep the vault for passwords and the vault for TOTP codes in different locations.
10. File Attachments
KeePassXC is not a replacement for VeraCrypt or Cryptomator, but you can store a few files in it.
Every file(s) you store in your KeePassXC goes in the one single file vault.
So if you have a few important files like your SSN card, driver’s license, or whatever you consider important, you can add them as attachments to your vault and they get encrypted with your master password.
You can also create multiple KeePassXC vaults to store these items if you need to. Combined with the default Argon2d and whatever encryption you pick, those files are quite secure. They may not be easy to get to if you went with VeraCrypt, but they sure are very secure.
Using KeePassXC as a way to store a few files is something I recommend when backing up your password manager.
For simple and a few small files, KeePassXC is a great way to store things securely.
What Password Manager Do Security Experts Use?
Security experts use all kinds of password managers; it comes down to personal preference.
If you want to know what a security expert that takes things to the extreme uses, then it will be KeePassXC.
Here is his podcast where he talks about using KeePassXC as his password manager. If you’re going to listen to anyone, then listen to this guy if you want the most secure anything.
Please Keep In Mind
Please keep in mind that the most secure password manager can’t protect you from malware or the $5 wrench attack.
Never open your vault on a computer you don’t 100% trust.
Keep your computer up to date and run some anti-virus software.
Since KeePassXC is a local password manager, you will be responsible for making backups of your vault.
For the average person, KeePassXC is way overkill and not the best password manager for you. For most, you would be better off with Bitwarden, 1Password, or any cloud password manager. Decide your threat level first before going with any password manager.
Store Cryptocurrencies In KeePassXC?
Overall, it’s best that you don’t store cryptocurrency seed phrases inside any password manager. A password manager is not immune to malware or the $5 wrench attack.
And in general, for the average person storing seed phrases on paper kept somewhere secure is the best option.
But if you had to store cryptocurrency seed phrases inside any password manager I would suggest KeePassXC.
Be sure to crank up the iterations and use a long and random master password.
For best results use a clean computer, maybe even a fresh install of Linux, and be sure to make plenty of backups of the KeePassXC file.
You can’t beat writing seed phrases down, so go with that for sure, but for the few that must do it digitally, KeePassXC is a good option.