A lot of misunderstanding and fear happened when ISE released their report that many of the top password managers were not as secure as many people hoped.
You can read their full report here.
First off, should you be worried? No. This threat level is so narrow. Let’s go over the issue and what you can do.
The Issue
The biggest issue is that people have a misunderstanding of how password managers work. Many people thought the password was always encrypted even when auto-filling into the website.
The truth is that your password needs to be in plain text at some point. Either viewing, editing, or auto-filling your password gets put into memory. This is normal for apps to do
The way many password managers went about this was worse than others. Many of them decrypt the entire vault into memory and even keep the master password in memory. This is not the best way to go about this, but it’s not as bad as it seems.
One valid concern was that some of these password managers did not clear out the memory when you locked the device. We’ve been told to think when it’s locked; it’s locked, but that was not the case for some.
Why would they allow this to happen? When programming there is a trade-off. You either write a program on a very low level which is very hard and more possibilities to make mistakes, or you write on a high level where you’re less likely to make mistakes and can fix things quicker. Most of the password managers companies go with the high-level programming and let the operating system and the programming language “helpers” do the cleanup and fix errors.
The cleanup time is where we have the issue. If you programmed
“You could perform the surgery on yourself, but it’s better to get someone who only does that particular procedure all the time to do it for you. “
You’ve Lost If Your Computer is Already Infected
If you’re using your password manager on a computer that is already infected, you’ve lost the game. It won’t matter how strong your password manager is at protecting your data because your machine is not yours anymore.
It’s like trying to drive your car underwater. There is no point, you’ve already lost.
This threat model is not new and seems to get debated every few years. Here is Google talking about this similar issue back in 2013.
Using Pen and Paper
My favorite response from people is that they either keep using pen and paper or switch to it. The people saying this have a misunderstanding of the threat.
I hate to break this to you but if your computer is infected even the pen and paper method is affected if not worse.
If they can read your memory, they can read your keystrokes. If you have to type in your password manually, they can either scoop it from memory like they could do with a password manager or steal it more efficiently via a keylogger.
What makes this worse is that the people who are more likely to write passwords down are more likely to reuse them. That is the real issue that password managers solve.
I’ll Use The Browser Instead
Another one that people seem to go to is that they’ll go back to using the web browser to store their passwords.
This is not a solution either. The browser is an app that suffers the same problems. If they can read the password manager memory, they can read the browser memory and get its passwords too.
Even worse is that browsers don’t take password security as seriously as password managers. There are ways you can read all your passwords from your browser without needing any passwords (Here, Here, and Here). You also notice this if you ever switch to a new browser and it allows you to export your passwords over – it does it without needing any password.
Why Use a Password Manager?
The real issue and why you need to use a password manager is that people reuse passwords. You’re more likely to get hacked by someone breaking into a website to steal passwords then someone getting your passwords from your single computer.
Since so many people reuse passwords, this means the hackers can use that one password many other places. A password manager helps to solve this problem by allowing you to create unique passwords for every account and then storing them for you.
Password reuse is a bigger problem than this memory issue that is for sure. If there ever comes a time when the memory issue becomes a more significant problem I’m more willing to bet the password manager companies have more on the line and would create new solutions before anyone else.
A Solution
What can you do?
Well, you should still use a password manager and give every account a unique password. Plus a password manager is the most convenient and secure way to do this.
One solution is to use 2 password managers — one for the important stuff and the other for everyday things.
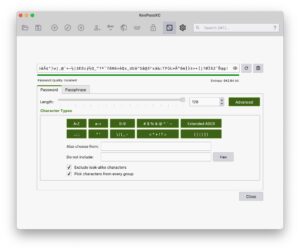
With password managers like KeePassXC, you can have multiple vaults each with their own master passwords.
How often are you logging into your banking or email accounts? Once you have Gmail logged in, you don’t need to log in much after that. Plus, with banking apps becoming easier to use do you really need to login on your desktop? Your mobile phone, especially if its an iPhone, is more locked down and thus more secure. So why not use your phone for only email and banking?
Then for your everyday accounts like Facebook, Reddit, Twitter, and so on you keep on the ready in a different password manager.
One option I like is to use a password manager like Bitwarden for my common passwords because its cloud-based. For the essential accounts use KeePassXC as its a local password manager and store it somewhere safe.
You could even go the route of keeping your banking and other essential passwords on pen and paper. Just make sure the passwords are unique and random. Then use a password manager for the everyday passwords.
Another option is to use 2FA more. I’m not talking about 2FA that sends you a text message with a code as that is not that secure. I’m talking OTP 2FA where you need to use Google Authenticator or Authy. Don’t store your 2FA codes in your password manager; even if the password manager becomes compromised they still need the 2FA code to get into the account.
Mac or Linux Affected?
Yes, but they handle it better.
A lot of this issue is because Windows doesn’t handle this that well. It’s really up to Windows when they do garbage collection of the memory. Also, putting safeguards or more tools to stop this attack is just as important.
I’m not saying Mac or Linux is better than Windows, but they have done more to protect users against this attack. (Technologies like XD (execute disable), Address Space Layout Randomization (ASLR), and Kernel ASLR make it difficult for malware to run or do harm by subverting memory or other apps.) There is only so
There is also only so much any operating system can do. If you want to login to a site, the password needs to be in plain text at one point to be able to fill in. There is nothing that exists that can protect you from that.
We Need Better
It boils down to we need something better. We can’t put all the blame on the programmers when they’re doing the best they can with the tools they have.
We need computer hardware manufacturers and operating systems to take security to a new level.
We need secure enclaves on every computer to better handle this type of stuff. A secure enclave won’t protect you from everything, but it sure is the step in the right direction.
We’re seeing more things like secure enclaves being put into smartphones because people take them more places so it has a higher risk of being stolen. While laptops and other computers are not carried around as much, we should not ignore them.
Think of a secure enclave as a computer inside of your computer. If the computer you work with becomes infected, the secure enclave computer is not affected. If you don’t deliver the correct responses to the secure enclave, it won’t talk to you. Since the little guy has few communications and only does basic things it’s less likely to become infected.
You can’t store passwords in them, but they can be used authenticate better than what we do now. Its the step in the right direction.
You can learn more about how Apple handles the secure enclave here.