What person in their right mind would enter their password into a site they don’t know?
That’s a fair point, but HaveIBeenPwned.com can check your password without ever knowing what it is.
How is that possible? Let me show you.
First Off
Before I go too deep into this, there is a super simple test you can take without telling anyone your password.
Answer the questions below.
- Have you ever used this password on more than one site?
- Is this your go-to password?
- Is your password something like your pets name, child’s name, address, or other personally related info?
- Do you have a password system where you use the name of the site with a formula?
If you answer yes to any of those questions, then it’s a good chance your password is in the https://haveibeenpwned.com/Passwords database.
There is one more test, and it’s even easier… If you’re afraid to enter your password in HaveIBeenPwned, then it means you’ve reused that password before. You’re scared to enter it because if you do then “they’ll know the password to other sites you use it on.”
If that is your fear, then there is no need to check HaveIBeenPwned. Your password is being reused on other sites which is a big no-no. Knowing this I’m very confident your password has been hacked before. Don’t believe me? Then let’s find out.
How HaveIBeenPwned Checks Your Password
Here are two great videos that goes over the same thing I show you below.
The magic of how HaveIBeenPwned can check your password without knowing it is because of K-Anonymity.
K-Anonymity is like spitting in a cup to submit a DNA sample. You don’t need your entire self, just a little bit of DNA to compare.
HaveIBeenPwned looks at the “DNA” of your password and reports back all the other “DNA” that is similar. Your browser looks at the other DNA to see if any of them match and if it does it prompts you.
While the DNA example explains it in a simple form, actually showing you how it works is even better.
Let Me Show You
There is going to be a lot of talk on hashing. I’ll give you a slight overview of it, but if you want to understand hashing more, please check out this video.
HaveIBeenPwned SHA1 hashes the password you give it. A hash is
If I hash “password” I get…
5BAA61E4C9B93F3F0682250B6CF8331B7EE68FD8
But I make a slight change like capitalize the first letter (“Password”) I would get this hash…
8BE3C943B1609FFFBFC51AAD666D0A04ADF83C9D
As you can see it makes an entirely different hash even though the change was small.
You can play with making hashes here… https://passwordsgenerator.net/sha1-hash-generator/
Hashing is what HaveIBeenPwned is doing when you submit your password.
For this example, I’m going to be checking “password” to see if it’s been any breaches.
How HaveIBeenPwned Works
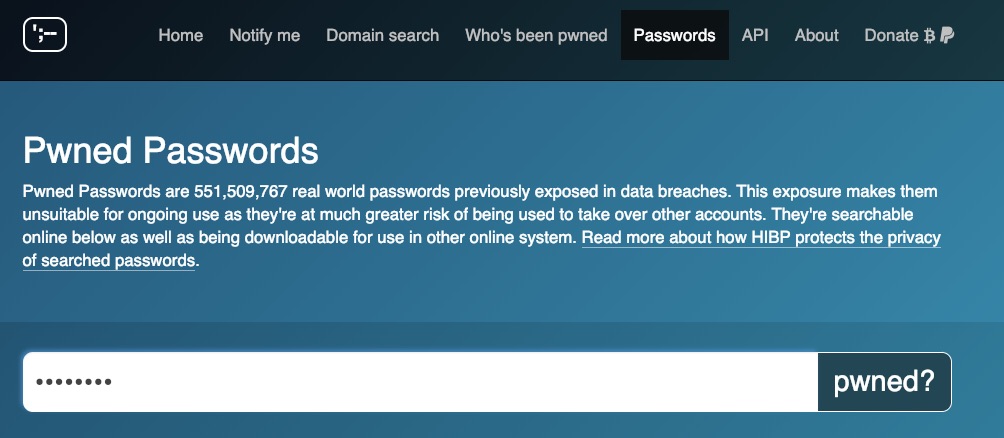
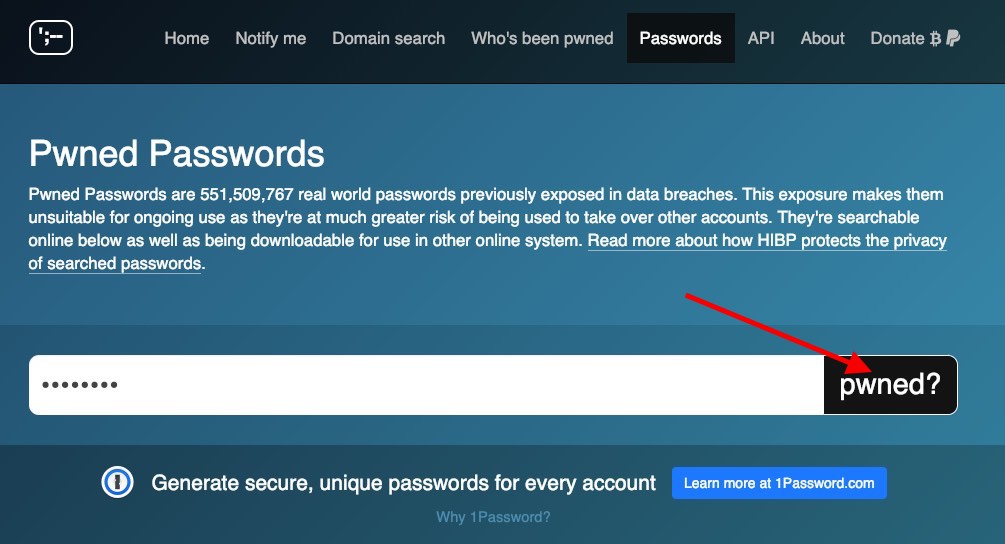
Right click on the page and select “Inspect.”
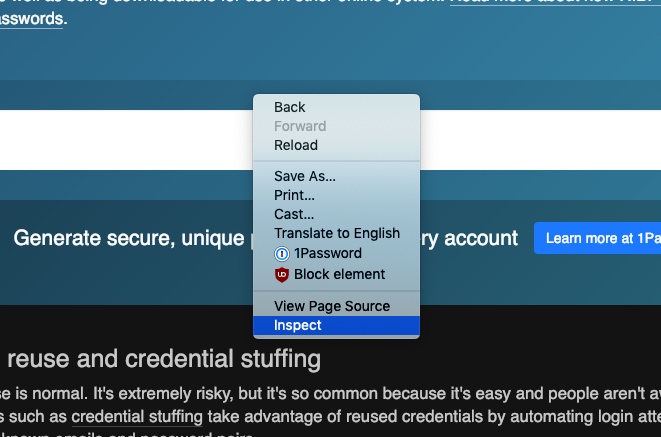
Select “Network” tab at the top. Then go back to the HaveIBeenPwned window.
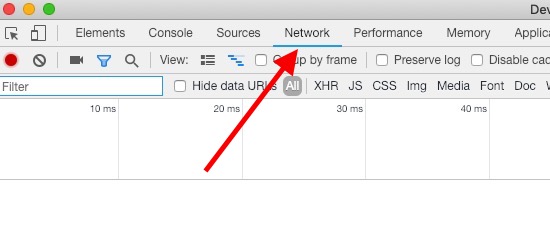
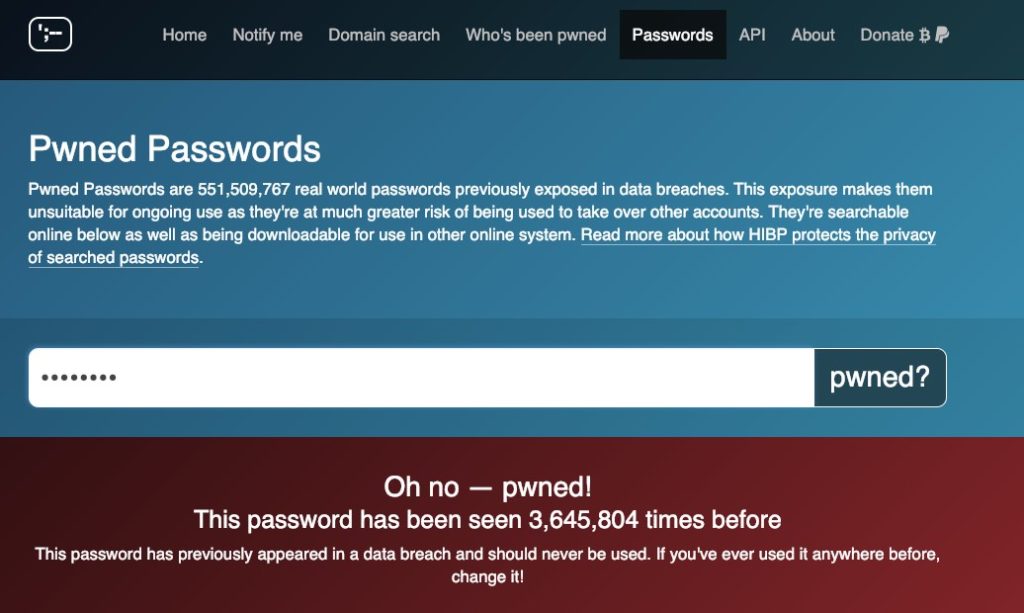
Enter your password into the field and press the “pwned?” button as shown below.
You’ll see if that password is pwned or not. “Pwned” in this case means the password was in a security breach and anyone can get to it, even hackers. It’s in your best interest to change that password immediately. In this example, “password” has been pwned.
Switch back over to the network window we opened earlier as shown below.
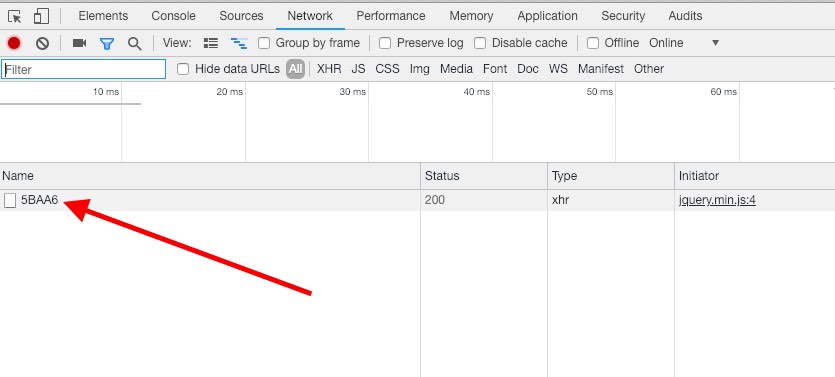
The “5BAA6” is the first 5 characters of the hash of “password” we submitted. If you submitted something else you’ll have 5 different characters. As pointed out earlier the entire hash was “5BAA61E4C9B93F3F0682250B6CF8331B7EE68FD8”. HaveIBeenPwned only takes the first 5 characters of the hash and sends it off to the server.
The server sends back all the hashes that start the same and then compares them inside your web browser.
When you click on the first 5 characters and select “Response” below you’ll see all the hashes the server sent to you.
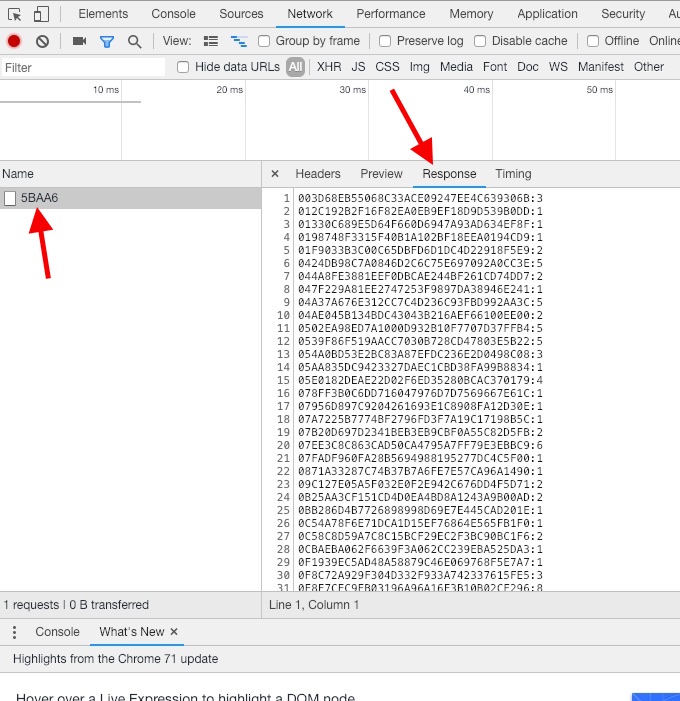
The first 5 characters of each hash are removed as they’re all the same. Then you have a “:” with a number next to that. The number next to the hash is how many times that password has been in a breach.
Pretty cool!
The only thing that is sent to HaveIBeenPwned is the first 5 characters of your 64 character hash of your password. The server sends back all the hashes that start with those first 5 hashes and your browser checks if there are any matches. If there is a match it uses the number next to the hash to let you know how many unique accounts have used that same password.
If your passwords show up just once you need to change it. The password is out in the public domain and it’s just a matter of time before someone gets into the account that uses that password.
Another Way To Check
There is another way to check your password. HaveIBeenPwned has an API which is just a fancy way of saying, “give me input I give you output.”
You’ll need a way to hash your password with SHA1. You can use this website to hash it. If you’re worried that they’ll steal your password, you can load the site and then turn off the wifi. Once you get all your SHA1 hashes, you can delete browser cookies and close the browser. Turn the wifi back on, and you’re ready to check those hashes.
In your web browser enter this into the address bar…
https://api.pwnedpasswords.com/range/At the end of the URL put the first 5 characters of your hashed password. It should look something like this…
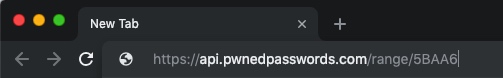
Hit enter to navigate to the page. You’ll get this…
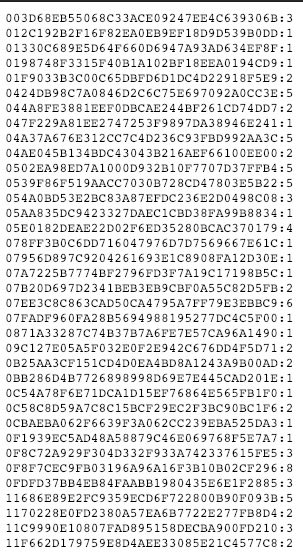
You get a wall of hashes along with the number next to them to tell you how many times that password has been seen.
To quickly search hit Ctrl+f (PC) or CMD+f (Mac) and enter the second half of the hash.
For example, my original hash was “5BAA61E4C9B93F3F0682250B6CF8331B7EE68FD8”. I would leave out the first 5 characters “5BAA6” and only search for “1E4C9B93F3F0682250B6CF8331B7EE68FD8”.
When I do that I see this
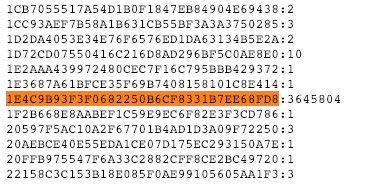
The hash of “password” has been seen 3,645,804 times before. That’s is a lot of people using that password.
There you have it. You now know that HaveIBeenPwned doesn’t collect your password and you can even check using the API to be even surer.
If you come this far, please donate HaveIBeenPwned. I don’t get paid to say that but as you can see it delivers a valuable service. Let’s keep it going!



The suggestion to disable Internet connection is a clever trick! I have always been wary of free “useful services” on the web, like the one described in this post (passwordsgenerator.net). This includes HIBP, but I can now more confidently submit my passwords to the service, knowing that they don’t get the complete hash. In fact, ever since HIBP was open sourced (last year), many companies – including Bitwarden and NordPass – have implemented it in their own password manager product for monitoring your accounts for data leaks and checking if your selected password has been seen in a data leak before. This uses the same k-anonimity model as described above.