Everywhere you go the number one advice you’ll get about securing an account is to use 2FA.
If you’re not aware, 2FA is two-factor authorization, also called two-step authorization. You either get a text message, email, or use an app that tells you what code to enter after your password. It’s like having a second password. Since the 2FA code continually changes, it’s not worth stealing, unlike a password.
I’m not going to argue that you’ll be better off without 2FA. Even the weakest of the 2FA, SMS text message, is still better than not having 2FA.
My issue with 2FA is that people forget the whole point of it and why we use it in the first place. There are also undesirable consequences of blindly pushing 2FA that are destroying its effectiveness and making some people less secure.
What’s The Point of 2FA?
The whole point of 2FA is if your 1FA (your password) is already known.
If you never reuse passwords, it makes 2FA pointless. Well, I guess a better word would be redundant.
Think of it like this – you have two locks on your door, one lock has a PIN and the other requires a Key (something you know and something you have). The PIN is like your password and the Key is your 2FA app. Where a lot of people go wrong is reusing passwords with their 2FA app. This would be like putting a sticky note with the PIN code next to the first lock – this is defeating the whole point of having two locks.
Most people don’t realize this issue and think since they have 2FA they’ll be fine which brings me to my first gripe with 2FA.
2FA Encourages Password Reuse
People are bad about reusing passwords. If you stop reusing passwords, you will prevent most, if not all, hacking attempts. Keyword being “most.”
When someone is “hacked,” the first thing to come out of people’s mouth is to turn on 2FA. While it will stop unauthorized access, it’s not solving the real problem.
The real problem is that they need to stop reusing passwords. Only turning on 2FA and doing nothing else is like jumping out of a plane knowing your first parachute will fail – who would do that?
If we blindly advise only turning on 2FA and doing nothing else the user will continue their path of reusing passwords.
Here is a great real example I’ve come across for this exact issue.
“I can’t stress how important 2FA is. I woke up to 56 requests from my authentication all because someone had been trying to get in.“ Archive. Another one.
Here is another one that is also a great example of this
I’m sitting on break at work and I’m watching the “Authy” app just send me 2FA request notifications one after the other. Scary knowing somebody wants my account that bad. But glad knowing that 2FA is doing it’s job in protecting my account.If it’s said once it’s said a million times but please if you haven’t enable 2 factor authentication I promise you the effort you put in is well worth the pay off of having a secure account. Archive.
These people were only ever told to turn on 2FA. No one told them to stop reusing passwords so they kept their bad password and still have hackers trying to get in. The problem is not solved because they’re getting multiple requests to log in. To a hacker seeing a screen requiring 2FA means the password works and the users reuses it so the hacker will move on to other sites to get in and steal what they need. And these poor people still have not solved their real issue of password reuse and now another account of there’s will get taken over where someone again will tell them to turn on 2FA and we repeat the vicious cycle til they get to a site that doesn’t have 2FA.
If we instead told them to give every account a unique password by using an app like a password manager, they would have solved the real issue and not use 2FA as a bandaid.
Plus, if we’re going to have people start to use 2FA apps, we might as well get them to use a password manager app first and solve the real issue. After addressing the underlying problem, they can then move on to hardening their accounts with 2FA.
2FA Doesn’t Make You Unhackable
2FA gets pushed as some magic cure to hacking.
That is false.
Here is the crazy part; someone could argue that some people are more hackable after enabling 2FA.
If you tell someone they can’t die because they now have this magic app, many will, unfortunately, believe you. They’ll start to do foolish things because they think they can’t get hurt.
This is how 2FA is being treated.
You start to drop your guard; you got 2FA now so no need to worry about getting hacked. Life is good! That is until you get a phishing page that steals your info.
And yes, 2FA can’t stop all phishing attacks.
Don’t believe me? Watch this video.
Hackers will send a phishing email that gets you to log in to what seems to be the legit site, that’s because it is. The hackers use a reverse proxy which acts more like a web browser.
They’re the middleman and once you login the site gives the “browser” a token so you (and now the hacker) can stay logged in. All this happens under a second, and since everyone made you think you’re safe because you have 2FA, you don’t pay any attention to the little things that are off. Once the hackers have the token, they don’t need your password or 2FA codes anymore. And yes, a VPN won’t protect you against this kind of attack.
2FA Doesn’t Stop Malware Attacks
Another point that gets overblown is that 2FA can protect you against malware.
This is not true either.
If your computer is infected, you’ve already lost the game; it’s not your computer anymore.
When the computer is infected, hackers can change how your computer responds to websites. If you go to Google.com, they could very easily change it to their phishing site and do the reverse proxy attack as I mentioned before.
Or they could steal the tokens already stored on your computer.
Another possibility is to use your computer as if they’re sitting in front of it. They have full access to the computer, and this is the holy grail for them. It’s much harder to dispute unauthorized charges if they’re coming from your computer.
A 2FA code that changes every 30 seconds won’t help you on a computer that is already infected. There are so many possibilities to get what they need that it doesn’t matter what you use. It’s like thinking you won’t explode on a minefield if you wear sandals – you’re playing a losing game no matter what you use.
Bruce Schneier agrees with me on this one.
2FA Won’t Help If The Service Gets Breached
If a website is already breached your password or 2FA won’t matter because they have full access anyway.
But this is not what they think when they say 2FA will protect you if a website gets breached.
This goes back to my point that 2FA encourages password reuse.
They’ve reused their password and think their other accounts will be fine because they have 2FA. What they forget is the other accounts that don’t have 2FA are now in trouble.
You never realize how many accounts you have until you get the email saying someone else has logged in and taken over that account. I used to think I had maybe 30 passwords; after I got my password manager, I slowly realized I had hundreds, and it still grows to this day.
Plus, reusing passwords because 2FA will save you is backwards thinking. Going back to my parachute metaphor, you don’t intentionally destroy the first parachute because the second one will save you. Why would you treat your online accounts this way?
The Other Drawback of 2FA
When talking about how great 2FA is the one thing people forget about is its biggest flaw.
You can turn off 2FA.
Here is one great real world example of the fact you can turn off 2FA…
Many services know customers will either lose their device with 2FA on it or do something where they can’t use it. So they’ll need a way to disable 2FA.
Some services like Apple do it the best by making users wait days, if not weeks, to turn it off after proving who they are.
Then there are far more services that do it all wrong and can turn it off with just an email or even worse answering some simple security question.
If all it took to turn off 2FA is knowing what high school you went to can we even claim 2FA is useful?
To give you an example, Steam allows you to turn off Steam Guard (2FA) so long as you know the password. If you can turn off 2FA just by simply knowing the 1FA (password) you never had 2FA; you instead had extra hoops to jump through to log in to your account.
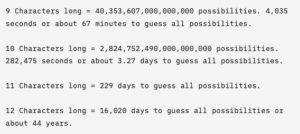
It will always boil down to using a unique password for every account. A unique password is far more important than 2FA.
So… Should We Even Use 2FA?
Yes, you should still use 2FA, but there is an order you must follow.
Before you even think about 2FA, you need to solve the 1FA problem first.
Step 1 – Stop reusing passwords. Get a password manager and give every account a unique password no matter how unimportant you think it is.
Step 2 – After the first step, you can do 2-Step (2FA). Get it?!?!?!
When Step 1 is done and you have given every account a unique password you can move onto setting up 2FA. You should only use 2FA to further harden the security of the account.
Never think of 2FA as protecting your account if your password is known but instead as more friction to logging into the account. The more friction you have the less desirable it becomes to steal.
Step 2.B – The fallback options a site has to turn off 2FA must also be considered. If all it takes to turn off 2FA is answering security questions should you bother with 2FA? If you have a genuinely unique password, I will argue it’s not worth having 2FA.
Don’t forget if the fallback option is to email you, it would be wise to make sure that email account has 2FA on and its fallback options are not easy to get around either.
Others Agree
A 2FA app is essentially a password manager. A 2FA seed/code is essentially a password. “Time-based” thing does not add any security, and 6-digits thing makes security even worse. 2FA is obscure, inconvenient, hard to backup, bruteforce-able password manager. You don’t need 2FA, all you need is a unique complex password and a password manager. https://sakurity.com/blog/2015/07/18/2fa.html