Security is important, especially in the digital world. Not many people realize this, but the software you use may not be as secure as they promise when a “lock” option is available.
There is a huge difference between something being password protected versus something being protected by encryption.
Just because something is protected by a password does not mean it’s secure. It also does not imply a password-protected item is better than something protected by encryption.
While a password is often used in encryption, the meanings of both are not the same.
Password Vs. Encryption
Something being protected by a password is the equivalent of having a bouncer to protect a door.
The bouncer will keep the wrong people out, but he’s not perfect either. The bouncer can be bribed, tricked, or simply bypassed.
Encryption, on the other hand, is the equivalent of a bank vault.
There is no one to bribe, trick or bypass; if you don’t have the key to get in, you’re not getting in.
If anything, encryption is stronger than comparing it to a bank vault because encryption transforms data into something else. It would be like a bank vault that scrambles the contents of the vault every time. So, even if you got in the vault, the contents are useless unless you know how to unscramble them.
Password Protection Is A Soft Lock
Most things that are password protected are a “soft lock”.
The soft lock will keep most honest people out, but if you have some skill, you can get around the lock.
For example, many computers have password protection on your login account. This will keep normal users out of your personal account, but it won’t stop someone who really wants in.
If you have an attacker who wants in your personal account on your computer but doesn’t know the password, they can simply extract the hard drive and just read your files.
The video below is about recovering files from a computer that won’t boot, but it’s the same process if someone wanted to get into your computer to see your files, but did not know the login password.
The way you stop an attacker from taking out your hard drive and reading your files is to encrypt the drive.
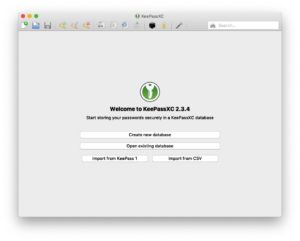
Encryption Is A Hard Lock
Encryption is a hard lock; there is no other way around it unless you know the correct password.
So if you encrypt your hard drive of your computer and an attacker gets a hold of it, they can’t simply take out the drive and read the files. The data is encrypted and looks like gibberish when they try to read it.
Unless the attacker knows the password, they won’t be able to unscramble the data.
Most Online Accounts Are Password Protected
Unless the website you use says they’re end-to-end encrypted, most websites are only password protected.
This means you need a password to get into your account, but nothing is stopping the person running the website from also being able to get into your account from the back-end.
We have even seen bugs in the past that would log you into someone else’s account, so something being password protected is not always the most secure. In 1999, Hotmail had a bug that allowed you to log into someone’s account with the password “eh”.
PDF Password Protected Vs. Encrypted
Of all the things to show the difference in password vs. encrypted protection, it would be the PDF.
A PDF that is password protected is not as strong as the PDF being encrypted.
The fact is that a PDF that is password protected can have the password removed doing some basic skills.
But if the PDF is encrypted, there is no way to bypass it unless you know the actual encryption password.
A PDF that is only password-protected is just a suggestion the software follows. If the software you use follows the rules, they will see that this file is password-protected, and the user must enter that before fully opening it. The thing is that other PDF readers can choose to ignore that and open the file.
If the PDF was encrypted, there is no ignoring it as the file is basically in a different language, and the software has no clue what to do with it. So, the software will notice that it’s encrypted and need the encryption password to descramble the data, so it’s readable.